Hideez Identity Provider Settings
Hideez Enterprise Server – Configuring HES as IdP
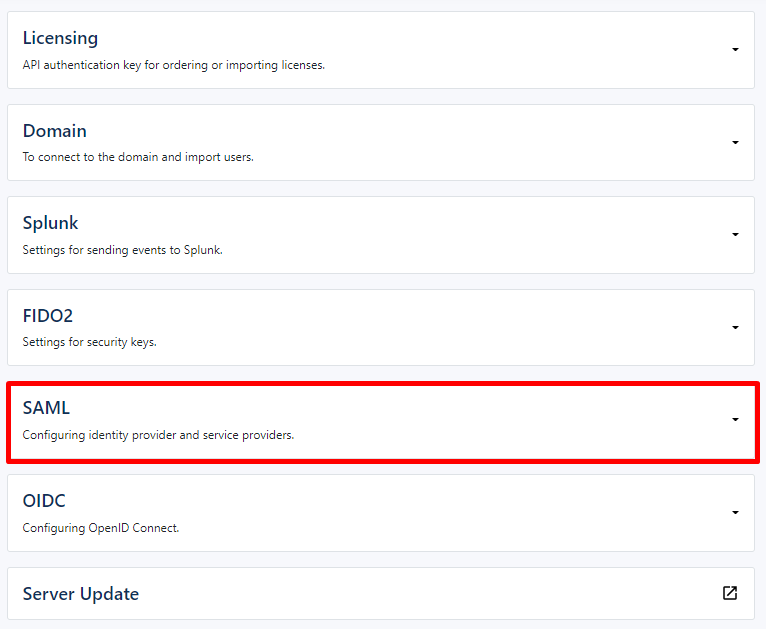
To access SAML settings, go to Settings -> Parameters -> SAML. SAML settings contains next sections: IdP metadata, IdP configuration (HES) and Service provider settings (third-party web applications).
Identity Provider configuration allows you to set and delete IdP settings.
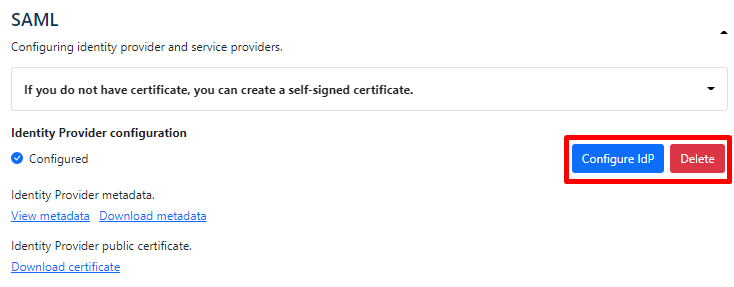
Also here you can get a script for creating a self-signed certificate. Just click the needed option.
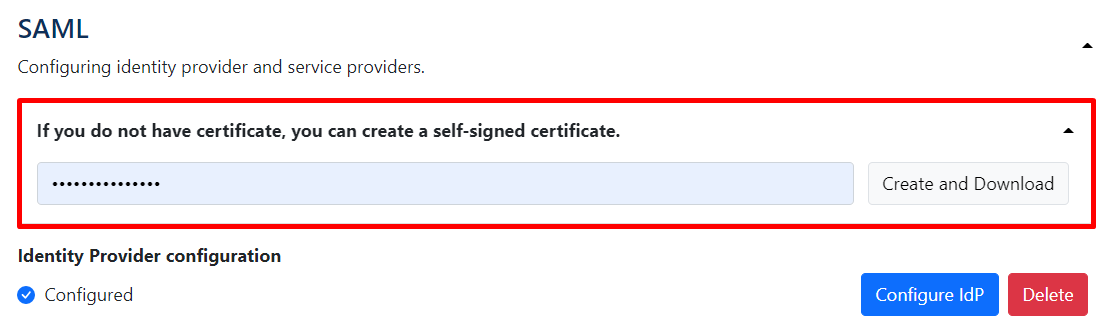
A certificate in the “.pfx” format is necessary for the work of the SAML protocol. It can be generated, for example, through an OpenSSL application or by using an existing certificate. The certificate file must be uploaded to the HES server. To do it, go on HES to the "Parameters" > "SAML" > "Configure IdP".
Here you need to set next parameters:
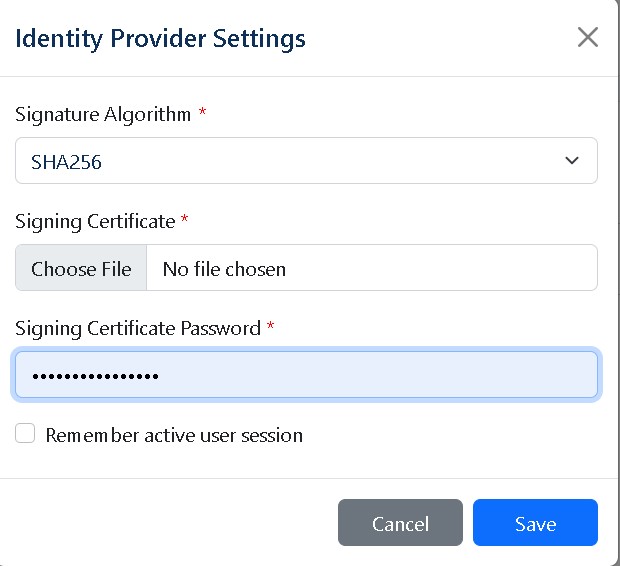
Signature Algorithm - a signature algorithm. It should match the algorithm with which the pfx certificate was established. The possible options are SHA1 / SHA256 / SHA384 / SHA512: SHA1: http://www.w3.org/2000/09/xmldsig#rsa-sha1 SHA256: http://www.w3.org/2001/04/xmldsig-more#rsa-sha256 SHA384: http://www.w3.org/2001/04/xmldsig-more#rsa-sha384 SHA512: http://www.w3.org/2001/04/xmldsig-more#rsa-sha512.
Signing Certificate File - the path to the certificate file.
Signing Certificate Password - the password to the certificate file.
Remember active user session - allows service provider to remember if user signed on HES or not.